Configuration of Digital Surveillance tools with real-time alerts on reputation and threats in the Dark and Deep Web.
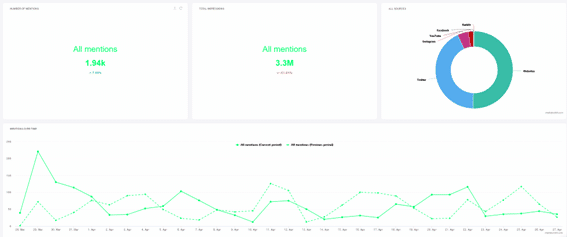
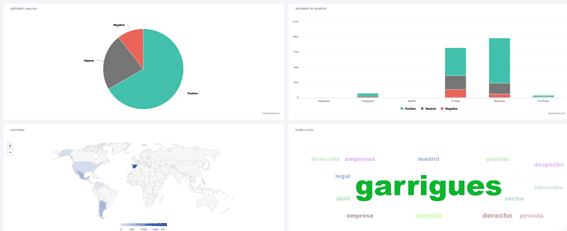
Garrigues is a firm that, by the very nature of its business, has a constant reputational risk associated with the reputation of the clients it represents. The situation prior to our entry into the client was based solely on an application for collecting mentions of the brand name. From our entry, they were able to have a service in which, apart from monitoring the elements they already had, they could add a greater cataloging of these alerts, as well as adding new features, such as review of password leaks, exposed corporate servers, blacklists, phishing, etc...
The resulting service could be divided into several areas depending on the client's department involved.
On the one hand, there are the marketing and communication departments, for which the reputation management service is offered.
On the other hand, there are the systems and security departments, which manage the exposure of users, systems and public networks in the clear, Deep and Dark Web.
Typically, our client reputation management service is based on finding the most important and negative news or mentions. When we joined the client Garrigues, we were faced with different requirements, since, working directly with the marketing team, they required a complete collection of every mention that appeared on the Internet. This fact led us to reinvent this service, changing the focus of the tools used because they needed alerts for every mention, and not only for the most relevant ones.
As a result of the actions carried out since the start of the service, Garrigues now has much more extensive monitoring of its brand exposure. Not only do they have mentions on the network, but they may also be able to detect in real time a possible identity theft, a phishing campaign against your company, elements of your architecture exposed, credentials leaked in massive hacks or appearances on the Dark Web among others.
SGoSat is a family of high-tech SOTM (Satellite Comms On The Move) terminals that are installed in a vehicle, providing the ability to target and maintain a stable connection to the satellite when the vehicle is in motion in any type of conditions.
The SGoSat family is composed of versatile terminals, which can be installed on any type of platform: trains and buses, military and/or government vehicles, aircraft, ships, etc. Originally designed for the military sector, SGoSat terminals are extremely reliable and robust, integrating high-performance components that comply with the most stringent environmental and EMI/EMC regulations. The product uses low-profile, high-efficiency antennas and a high-performance positioning and tracking unit, allowing the terminal to be operated anywhere in the world.
In order to meet the diverse needs of its customers, INSTER has developed single band and dual band terminals in X, Ka and Ku frequencies.
The SGoSat family of terminals can also be configured with a wide range of radomes (including ballistic options) to suit customer requirements.